Loxe AI
Automated SOC 2 compliance with an AI security analyst that scans cloud posture and streams Terraform remediation.
Next.jsTypeScriptPrismaPostgreSQLPythonAWSTerraform
Role: Founder & Software Engineer • Spring 2026 – Present
Traction
Paid pilot
Moved from PoC → revenue
System
AWS posture scan
IAM/S3 signals + checks
Output
Terraform remediation
AI streams actionable fixes
Problem
Teams spend significant time gathering evidence, mapping controls, and translating findings into concrete remediation. I wanted a workflow that is automated, auditable, and easy to act on.
Approach
- Built a full-stack compliance workflow (Next.js/TypeScript + Prisma/PostgreSQL).
- Implemented a Python scanning engine that inspects AWS posture and extracts compliance signals.
- Added an AI analyst that summarizes risk, prioritizes issues, and streams Terraform remediation.
- Focused on clear outputs: what is wrong, why it matters, and what to change.
Media
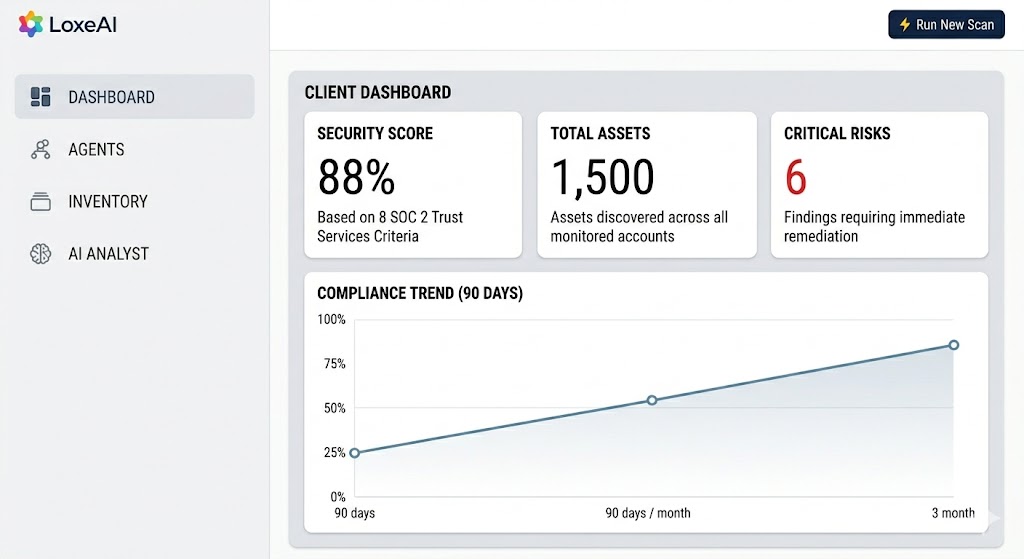
Product dashboard (sanitized).
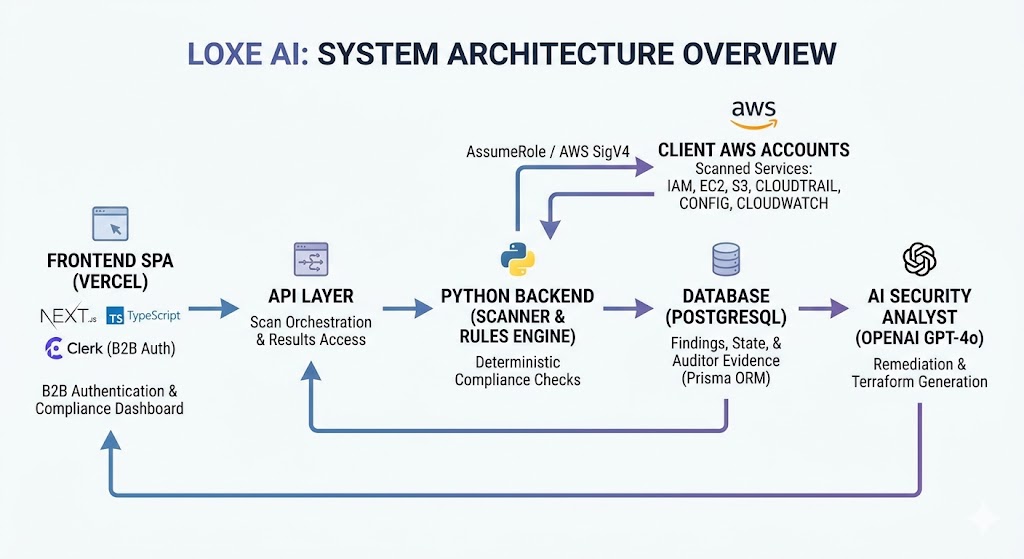
System architecture: frontend → API → scanner → DB → AI analyst.
30–60s walkthrough of scan → findings → Terraform remediation (sanitized).
Results
- Shipped an end-to-end product workflow from onboarding to findings and reporting.
- Closed a paid pilot to validate the workflow and move toward revenue.
- Built repeatable scanning + reporting primitives that generalize across accounts.
Lessons / Next
- Security tooling only works if outputs are actionable and low-friction.
- The hardest part is not generation—it’s reliable data collection + validation.
- Next: expand coverage of checks, improve evaluation harness, and harden the scanning pipeline.